A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle...
48 KB (6,237 words) - 00:38, 5 November 2024
derived from a hash function which takes a data input and returns a fixed length of bits. Although hash algorithms, especially cryptographic hash algorithms...
9 KB (1,130 words) - 16:51, 9 August 2024
This is a list of hash functions, including cyclic redundancy checks, checksum functions, and cryptographic hash functions. Adler-32 is often mistaken...
10 KB (280 words) - 12:41, 17 October 2024
BLAKE is a cryptographic hash function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants...
30 KB (2,848 words) - 05:59, 18 August 2024
general and technical information for a number of cryptographic hash functions. See the individual functions' articles for further information. This article...
16 KB (806 words) - 20:08, 6 August 2024
password, or a passphrase using a pseudorandom function (which typically uses a cryptographic hash function or block cipher). KDFs can be used to stretch...
13 KB (1,641 words) - 06:40, 27 October 2024
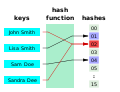
output. The values returned by a hash function are called hash values, hash codes, hash digests, digests, or simply hashes. The values are usually used to...
50 KB (7,445 words) - 00:27, 29 October 2024
HMAC (redirect from Keyed-Hashing Message Authentication)
of message authentication code (MAC) involving a cryptographic hash function and a secret cryptographic key. As with any MAC, it may be used to simultaneously...
18 KB (2,335 words) - 04:57, 18 October 2024
Preimage attack (redirect from Hash function preimage)
cryptography, a preimage attack on cryptographic hash functions tries to find a message that has a specific hash value. A cryptographic hash function...
7 KB (895 words) - 15:44, 13 April 2024
(or FNV) is a non-cryptographic hash function created by Glenn Fowler, Landon Curt Noll, and Kiem-Phong Vo. The basis of the FNV hash algorithm was taken...
15 KB (1,358 words) - 21:27, 19 October 2024
In computer science and cryptography, Whirlpool (sometimes styled WHIRLPOOL) is a cryptographic hash function. It was designed by Vincent Rijmen (co-creator...
11 KB (1,054 words) - 03:57, 19 March 2024
other cryptographic primitives); in this case they are described as universal hash functions. Among the typical uses of non-cryptographic hash functions are...
7 KB (796 words) - 04:17, 23 August 2024
In cryptography, a salt is random data fed as an additional input to a one-way function that hashes data, a password or passphrase. Salting helps defend...
13 KB (1,533 words) - 23:19, 23 October 2024
The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S...
3 KB (464 words) - 07:05, 4 October 2024
In cryptography, cryptographic hash functions can be divided into two main categories. In the first category are those functions whose designs are based...
13 KB (1,811 words) - 20:15, 26 August 2024
to a spate of "hash flooding" denial-of-service attacks (HashDoS) in late 2011. SipHash is designed as a non-cryptographic hash function. Although it can...
14 KB (1,342 words) - 05:08, 21 August 2024
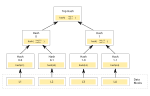
Merkle tree (redirect from Tiger-Tree Hash)
In cryptography and computer science, a hash tree or Merkle tree is a tree in which every "leaf" node is labelled with the cryptographic hash of a data...
15 KB (1,788 words) - 20:42, 10 September 2024
The MD2 Message-Digest Algorithm is a cryptographic hash function developed by Ronald Rivest in 1989. The algorithm is optimized for 8-bit computers....
9 KB (1,053 words) - 18:49, 15 September 2024
Sponge functions have both theoretical and practical uses. They can be used to model or implement many cryptographic primitives, including cryptographic hashes...
7 KB (811 words) - 14:51, 1 November 2024
known attacks against cryptographic hash functions. Note that not all entries may be up to date. For a summary of other hash function parameters, see comparison...
17 KB (1,055 words) - 12:18, 2 March 2023
not limited to, one-way hash functions and encryption functions. When creating cryptographic systems, designers use cryptographic primitives as their most...
6 KB (814 words) - 02:12, 9 May 2024
Message authentication code (redirect from Keyed hash function)
MAC algorithms can be constructed from other cryptographic primitives, like cryptographic hash functions (as in the case of HMAC) or from block cipher...
16 KB (1,914 words) - 13:54, 20 October 2024
and so has been thought worth the effort. Cryptographic hash functions are a third type of cryptographic algorithm. They take a message of any length...
98 KB (10,723 words) - 20:16, 2 November 2024
In cryptography, a pepper is a secret added to an input such as a password during hashing with a cryptographic hash function. This value differs from...
8 KB (1,045 words) - 17:11, 6 November 2024
Avalanche effect (redirect from Avalanche (cryptography))
In cryptography, the avalanche effect is the desirable property of cryptographic algorithms, typically block ciphers and cryptographic hash functions, wherein...
5 KB (568 words) - 17:23, 14 December 2023
Hash-based cryptography is the generic term for constructions of cryptographic primitives based on the security of hash functions. It is of interest as...
20 KB (2,329 words) - 09:31, 3 September 2024
In cryptography, Tiger is a cryptographic hash function designed by Ross Anderson and Eli Biham in 1995 for efficiency on 64-bit platforms. The size of...
9 KB (910 words) - 14:47, 30 September 2023
Merkle–Damgård construction (redirect from Merkle-Damgard hash function)
In cryptography, the Merkle–Damgård construction or Merkle–Damgård hash function is a method of building collision-resistant cryptographic hash functions...
15 KB (1,904 words) - 18:20, 19 September 2024
Security level (redirect from Broken hash function)
In cryptography, security level is a measure of the strength that a cryptographic primitive — such as a cipher or hash function — achieves. Security level...
13 KB (1,338 words) - 15:29, 6 November 2024