that are 224, 256, 384 or 512 bits: SHA-224, SHA-256, SHA-384, SHA-512, SHA-512/224, SHA-512/256. SHA-256 and SHA-512 are novel hash functions whose digests...
51 KB (4,975 words) - 05:28, 14 November 2024
against SHA-1 are practical. As such, it is recommended to remove SHA-1 from products as soon as possible and instead use SHA-2 or SHA-3. Replacing SHA-1 is...
50 KB (5,744 words) - 19:28, 20 October 2024
of the same series of standards, SHA-3 is internally different from the MD5-like structure of SHA-1 and SHA-2. SHA-3 is a subset of the broader cryptographic...
52 KB (5,765 words) - 00:56, 20 November 2024
Secure Hash Algorithms (redirect from SHA family)
SHA), FIPS PUB 180-1 (SHA-1), FIPS PUB 180-2 (SHA-1, SHA-256, SHA-384, and SHA-512). NIST has updated Draft FIPS Publication 202, SHA-3 Standard separate...
3 KB (464 words) - 07:05, 4 October 2024
Cryptographic hash function (section SHA-2)
Documents may refer to SHA-1 as just "SHA", even though this may conflict with the other Secure Hash Algorithms such as SHA-0, SHA-2, and SHA-3. RIPEMD (RACE...
48 KB (6,237 words) - 01:51, 13 November 2024
HMAC (redirect from HMAC-SHA-256)
key prior to communication. Any cryptographic hash function, such as SHA-2 or SHA-3, may be used in the calculation of an HMAC; the resulting MAC algorithm...
18 KB (2,327 words) - 04:57, 18 October 2024
Sha Sha is the debut album by American indie rock singer, songwriter, multi-instrumentalist and former Radish member Ben Kweller. The album was originally...
7 KB (511 words) - 19:08, 1 September 2024
MD5, SHA-1 and most of SHA-2 that are based on the Merkle–Damgård construction are susceptible to this kind of attack. Truncated versions of SHA-2, including...
7 KB (1,046 words) - 12:26, 6 June 2024
Simple Network Management Protocol (section Version 2)
(Proposed|Historic) — HMAC-SHA-2 Authentication Protocols in the User-based Security Model (USM) for SNMPv3 RFC 7860 (Proposed) — HMAC-SHA-2 Authentication Protocols...
40 KB (5,028 words) - 15:08, 17 November 2024
NIST hash function competition (redirect from SHA-3 competition)
function called SHA-3 to complement the older SHA-1 and SHA-2. The competition was formally announced in the Federal Register on November 2, 2007. "NIST...
27 KB (2,244 words) - 20:34, 28 February 2024
Windows Server 2008 (redirect from Windows Server 2008 Service Pack 2)
Windows updates with the SHA-2 algorithm. As a result of this Microsoft released several updates throughout 2019 to add SHA-2 signing support to Windows...
54 KB (4,949 words) - 21:55, 7 November 2024
Tsim Sha Tsui (Chinese: 尖沙咀), often abbreviated as TST, is an area in southern Kowloon, Hong Kong. The area is administratively part of the Yau Tsim Mong...
24 KB (2,788 words) - 06:09, 23 November 2024
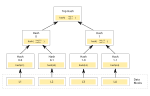
child nodes under each node. Usually, a cryptographic hash function such as SHA-2 is used for the hashing. If the hash tree only needs to protect against...
15 KB (1,788 words) - 20:42, 10 September 2024
Shas (Hebrew: ש״ס) is a Haredi religious political party in Israel. Founded in 1984 under the leadership of Rabbi Ovadia Yosef, a former Israeli Sephardi...
37 KB (3,016 words) - 07:16, 23 November 2024
for further use", and most U.S. government applications now require the SHA-2 family of hash functions. In 2012, the Flame malware exploited the weaknesses...
47 KB (4,712 words) - 21:30, 30 August 2024
block, XORed with round constants, is added before each ChaCha round. Like SHA-2, there are two variants differing in the word size. ChaCha operates on a...
30 KB (2,848 words) - 05:59, 18 August 2024
Dogrel (redirect from Sha Sha Sha)
9) Tom Coll – drums (1–11), tambourine (8, 10), miscellaneous percussion (2) Conor Deegan – bass guitar (1–11), piano (4), baritone guitar (5), surf guitar...
14 KB (1,047 words) - 07:02, 3 February 2024
e={\textrm {HASH}}(m)} . (Here HASH is a cryptographic hash function, such as SHA-2, with the output converted to an integer.) Let z {\displaystyle z} be the...
19 KB (2,833 words) - 03:20, 18 September 2024
sha512sum, which use a specific SHA-2 hash function and b2sum, which uses the BLAKE2 cryptographic hash function. The SHA-1 variants are proven vulnerable...
6 KB (577 words) - 11:01, 27 September 2023
Diffie–Hellman and Elliptic Curve Digital Signature Algorithm with curve P-384 SHA-2 with 384 bits, Diffie–Hellman key exchange with a minimum 3072-bit modulus...
9 KB (635 words) - 23:58, 26 August 2024
Sha Na Na was an American rock and roll and doo-wop revival group formed in 1969. The group performed a song-and-dance repertoire based on 1950s hit songs...
35 KB (4,241 words) - 21:18, 4 November 2024
result is necessary. While RIPEMD functions are less popular than SHA-1 and SHA-2, they are used, among others, in Bitcoin and other cryptocurrencies...
9 KB (857 words) - 20:38, 29 May 2024
('md5crypt') $2$: Blowfish-based crypt ('bcrypt') $sha1$: SHA-1-based crypt ('sha1crypt') $5$: SHA-256-based crypt ('sha256crypt') $6$: SHA-512-based crypt...
27 KB (2,833 words) - 15:52, 8 November 2024
Kong. Administratively, it is part of the Sha Tin District. Sha Tin is one of the neighbourhoods of the Sha Tin New Town project. The new town was founded...
29 KB (2,669 words) - 22:35, 5 November 2024
compatibility with protocols assuming a particular hash size. Unlike the SHA-2 family, no distinguishing initialization values are defined; they are simply...
9 KB (910 words) - 14:47, 30 September 2023
MD5, but cryptanalysts have identified attacks against it; the SHA-2 family improves on SHA-1, but is vulnerable to clashes as of 2011; and the US standards...
99 KB (10,933 words) - 18:36, 19 November 2024
bitcoin investor Roger Ver provided initial funding. By October 2014, it had 2.3 million consumer wallets and raised $30.5 million in its first external...
20 KB (1,798 words) - 04:21, 26 July 2024
was used in the design of many popular hash algorithms such as MD5, SHA-1, and SHA-2. The Merkle–Damgård construction was described in Ralph Merkle's Ph...
15 KB (1,904 words) - 18:20, 19 September 2024
Sha Ra is an Indian actor has worked predominantly in Tamil films. Shah Ra did his schooling at Laurel High Secondary School, Pattukkottai. He complete...
8 KB (335 words) - 22:28, 10 November 2024
competition. Entered as a candidate to become the SHA-3 standard, the successor of SHA-1 and SHA-2, it ultimately lost to NIST hash candidate Keccak....
9 KB (836 words) - 02:45, 11 July 2024