Differential cryptanalysis Harvest now, decrypt later Impossible differential cryptanalysis Improbable differential cryptanalysis Integral cryptanalysis Linear...
44 KB (5,215 words) - 23:06, 12 September 2024
Differential cryptanalysis is a general form of cryptanalysis applicable primarily to block ciphers, but also to stream ciphers and cryptographic hash...
13 KB (1,688 words) - 16:36, 5 September 2024
In cryptography, linear cryptanalysis is a general form of cryptanalysis based on finding affine approximations to the action of a cipher. Attacks have...
6 KB (812 words) - 13:20, 1 November 2023
differential cryptanalysis. The term "rotational cryptanalysis" was coined by Dmitry Khovratovich and Ivica Nikolić in 2010 paper "Rotational Cryptanalysis of ARX"...
3 KB (309 words) - 01:31, 3 May 2024
Cryptography (section Cryptanalysis)
letter, a syllable, or a pair of letters, etc.) to produce a cyphertext. Cryptanalysis is the term used for the study of methods for obtaining the meaning...
98 KB (10,713 words) - 06:06, 10 September 2024
less complexity than a brute-force search: differential cryptanalysis (DC), linear cryptanalysis (LC), and Davies' attack. However, the attacks are theoretical...
59 KB (6,541 words) - 09:32, 30 July 2024
cryptanalysis is a type of side channel attack that exploits sounds emitted by computers or other devices. Most of the modern acoustic cryptanalysis focuses...
10 KB (1,020 words) - 00:43, 20 September 2023
History of cryptography (redirect from History of cryptanalysis)
development of cryptography has been paralleled by the development of cryptanalysis — the "breaking" of codes and ciphers. The discovery and application...
51 KB (6,701 words) - 20:38, 1 September 2024
cryptanalysis is a form of cryptanalysis for block ciphers. Developed by Carlo Harpes in 1995, the attack is a generalization of linear cryptanalysis...
4 KB (379 words) - 00:39, 26 January 2021
Deniable encryption (redirect from Rubber-hose cryptanalysis)
have done what they can to recover a key. In cryptography, rubber-hose cryptanalysis is a euphemism for the extraction of cryptographic secrets (e.g. the...
24 KB (2,832 words) - 16:35, 5 September 2024
Frequency analysis (redirect from Frequency analysis (cryptanalysis))
In cryptanalysis, frequency analysis (also known as counting letters) is the study of the frequency of letters or groups of letters in a ciphertext. The...
16 KB (1,663 words) - 06:05, 8 April 2024
Cryptanalysis of the Enigma ciphering system enabled the western Allies in World War II to read substantial amounts of Morse-coded radio communications...
138 KB (17,741 words) - 21:17, 15 August 2024
cryptography, mod n cryptanalysis is an attack applicable to block and stream ciphers. It is a form of partitioning cryptanalysis that exploits unevenness...
3 KB (412 words) - 04:42, 1 July 2023
Known-plaintext attack (redirect from Crib (cryptanalysis))
guessing if there are fewer than 26 distinct pairs. Cadix Cryptanalysis of the Enigma Kiss (cryptanalysis) PC Bruno Polish Cipher Bureau Ultra (cryptography)...
10 KB (1,286 words) - 22:00, 7 January 2024
In cryptanalysis, gardening is the act of encouraging a target to use known plaintext in an encrypted message. It was a term used at the British Government...
3 KB (338 words) - 12:32, 13 June 2024
In cryptanalysis, a kiss is a pair of identical messages sent using different ciphers, one of which has been broken. The term was used at Bletchley Park...
1 KB (133 words) - 07:29, 5 September 2024
Block cipher (section Cryptanalysis)
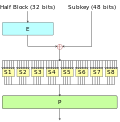
A linear cryptanalysis is a form of cryptanalysis based on finding affine approximations to the action of a cipher. Linear cryptanalysis is one of the...
50 KB (6,475 words) - 03:59, 22 August 2024
and Dmitry Khovratovich, Related-key Cryptanalysis of the Full AES-192 and AES-256, "Related-key Cryptanalysis of the Full AES-192 and AES-256". Table...
49 KB (5,595 words) - 00:02, 27 August 2024
Twofish (section Cryptanalysis)
2000[update], the best published cryptanalysis of the Twofish block cipher is a truncated differential cryptanalysis of the full 16-round version. The...
9 KB (841 words) - 21:49, 2 August 2024
Military Cryptanalytics (redirect from Military Cryptanalysis)
ISBN 0-89412-076-X Military Cryptanalysis, Part I, ISBN 0-89412-044-1 Military Cryptanalysis, Part II, ISBN 0-89412-064-6 Military Cryptanalysis, Part III, Simpler...
5 KB (590 words) - 01:00, 25 July 2022
NXT). Unlike differential cryptanalysis, which uses pairs of chosen plaintexts with a fixed XOR difference, integral cryptanalysis uses sets or even multisets...
8 KB (716 words) - 11:40, 5 September 2023
the head of the department Arne Beurling Bletchley Park Cryptanalysis of the Enigma Cryptanalysis of the Lorenz cipher Far East Combined Bureau (FECB) Naval...
6 KB (624 words) - 11:48, 12 August 2024
is usually encrypted, signals intelligence may necessarily involve cryptanalysis (to decipher the messages). Traffic analysis—the study of who is signaling...
54 KB (6,786 words) - 15:56, 25 August 2024
Playfair cipher (section Cryptanalysis)
United States Army. Another cryptanalysis of a Playfair cipher can be found in Chapter XXI of Helen Fouché Gaines' Cryptanalysis / a study of ciphers and...
20 KB (2,502 words) - 18:18, 12 September 2024
Skipjack (cipher) (section Cryptanalysis)
than exhaustive search) within months using impossible differential cryptanalysis. A truncated differential attack was also published against 28 rounds...
12 KB (1,080 words) - 02:34, 19 July 2024
Cryptanalysis of the Lorenz cipher was the process that enabled the British to read high-level German army messages during World War II. The British Government...
81 KB (8,714 words) - 12:51, 26 May 2024
In cryptography, truncated differential cryptanalysis is a generalization of differential cryptanalysis, an attack against block ciphers. Lars Knudsen...
4 KB (318 words) - 04:35, 17 October 2023
Contact analysis (redirect from Contact analysis (cryptanalysis))
In cryptanalysis, contact analysis is the study of the frequency with which certain symbols precede or follow other symbols. The method is used as an...
2 KB (364 words) - 00:42, 30 January 2024
Eli Biham (section Contributions to cryptanalysis)
iacr.org. Biham, E., & Perle, S. (2018). Conditional Linear Cryptanalysis – Cryptanalysis of DES with Less Than 242 Complexity. IACR Transactions on Symmetric...
4 KB (348 words) - 05:39, 14 May 2024
Transposition cipher (section Cryptanalysis)
immediately with cryptanalysis techniques. Transposition ciphers have several vulnerabilities (see the section on "Detection and cryptanalysis" below), and...
25 KB (3,604 words) - 03:23, 21 March 2024