Quantum key distribution (QKD) is a secure communication method that implements a cryptographic protocol involving components of quantum mechanics. It...
102 KB (11,755 words) - 05:38, 20 December 2024
cryptography is quantum key distribution, which offers an information-theoretically secure solution to the key exchange problem. The advantage of quantum cryptography...
81 KB (9,043 words) - 18:03, 20 December 2024
Quantum key distribution (QKD) protocols are used in quantum key distribution. The first protocol of that kind was BB84, introduced in 1984 by Charles...
5 KB (720 words) - 06:35, 18 August 2024
development of quantum computing, quantum communication and quantum sensing. Quantum computing and communication are two sub-fields of quantum information...
47 KB (2,014 words) - 21:33, 16 December 2024
applications of quantum cryptography is quantum key distribution which provide a theoretical solution to the security issue of a classical key. The advantage...
41 KB (4,542 words) - 01:00, 10 October 2024
require only very modest quantum processors. For most quantum internet protocols, such as quantum key distribution in quantum cryptography, it is sufficient...
54 KB (6,257 words) - 15:36, 7 December 2024
demonstration of BB84 quantum key distribution in optical aircraft downlinks. Airborne demonstration of a quantum key distribution receiver payload. Communication...
12 KB (1,378 words) - 07:56, 9 December 2024
October 8, 2008 SECOQC was launched in Vienna. Quantum cryptography, usually known as quantum key distribution (QKD) provides powerful security. But it has...
3 KB (354 words) - 17:14, 29 January 2024
High-dimensional quantum key distribution (HDQKD) is a technology for secure communication between two parties. It allows for higher information efficiency...
2 KB (229 words) - 03:54, 9 July 2023
applied quantum theory to cryptography protocols and demonstrated that quantum key distribution could enhance information security. Quantum algorithms...
115 KB (12,563 words) - 14:41, 14 December 2024
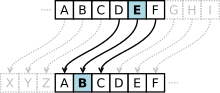
BB84 (category Quantum information science)
BB84 is a quantum key distribution scheme developed by Charles Bennett and Gilles Brassard in 1984. It is the first quantum cryptography protocol. The...
8 KB (1,098 words) - 05:06, 18 November 2024
public-key algorithms) that are currently thought to be secure against a cryptanalytic attack by a quantum computer. Most widely-used public-key algorithms...
62 KB (6,486 words) - 11:44, 12 December 2024
One-time pad (redirect from One time key)
equals the size of the pad. Quantum key distribution also proposes a solution to this problem, assuming fault-tolerant quantum computers. Distributing very...
57 KB (7,613 words) - 09:47, 6 October 2024
for quantum key distribution and randomness expansion. Action at a distance Popper's experiment Quantum pseudo-telepathy Quantum contextuality Quantum foundations...
65 KB (9,418 words) - 05:57, 11 November 2024
European receiving stations. The satellite conducted Space-Earth quantum key distribution (Chinese: 量子密钥分发) experiments, facilitated by laser communications...
23 KB (1,947 words) - 20:10, 22 December 2024
In quantum computing, quantum supremacy or quantum advantage is the goal of demonstrating that a programmable quantum computer can solve a problem that...
54 KB (5,929 words) - 15:08, 12 December 2024
later influenced the development of quantum key distribution protocols used in quantum cryptography. Wiesner's quantum money scheme was first published in...
4 KB (534 words) - 23:49, 20 March 2024
This list contains quantum processors, also known as quantum processing units (QPUs). Some devices listed below have only been announced at press conferences...
41 KB (1,858 words) - 04:26, 19 December 2024
using methods such as Shor's algorithm. These methods include quantum key distribution (QKD), a method of transmitting information using entangled light...
21 KB (2,218 words) - 04:44, 19 December 2024
ID Quantique (category Quantum cryptography)
company, based in Geneva, Switzerland, and provides quantum key distribution (QKD) systems, quantum safe network encryption, single photon counters, and...
8 KB (759 words) - 03:51, 31 July 2024
The DARPA Quantum Network (2002–2007) was the world's first quantum key distribution (QKD) network, operating 10 optical nodes across Boston and Cambridge...
10 KB (1,261 words) - 13:54, 25 April 2024
verification bottleneck only for the medium term, as BLS signatures are not quantum secure. Over the longer term—say, 2025–2030—STARK aggregation is expected...
8 KB (950 words) - 05:35, 23 November 2024
additional conditions regard implementing quantum communication, such as that used in quantum key distribution. One can demonstrate that DiVincenzo's criteria...
14 KB (1,815 words) - 21:57, 15 November 2024
publishing a quantum key distribution protocol called E91 based on it.: 874 In 1992, the entanglement concept was leveraged to propose quantum teleportation...
113 KB (13,590 words) - 21:30, 22 December 2024
to do. Most modern symmetric-key algorithms appear to be resistant to the threat of post-quantum cryptography. Quantum computers would exponentially...
15 KB (1,544 words) - 12:46, 16 December 2024
technologies, such as Quantum computing, Quantum key distribution and Quantum metrology. Photons are particularly attractive carriers of quantum information due...
37 KB (4,199 words) - 00:20, 7 June 2024
Arguments in the WHERE clause of a SQL database query. SARG04, a quantum key distribution protocol Tony Sarg (1880–1942), German-American puppeteer and illustrator...
471 bytes (80 words) - 17:29, 20 July 2015
frequency distribution of the letters. By graphing the frequencies of letters in the ciphertext, and by knowing the expected distribution of those letters...
19 KB (2,058 words) - 20:52, 22 December 2024
In quantum computing, a quantum algorithm is an algorithm that runs on a realistic model of quantum computation, the most commonly used model being the...
39 KB (4,558 words) - 00:09, 21 November 2024
concerns about the need to urgently deploy post-quantum cryptography, even though no practical quantum attacks yet exist, as some data stored now may still...
4 KB (325 words) - 13:45, 14 December 2024