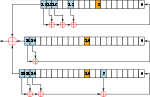
In cryptography, ciphertext stealing (CTS) is a general method of using a block cipher mode of operation that allows for processing of messages that are...
17 KB (2,269 words) - 14:13, 13 January 2024
universal LRW/XEX/GCM hardware. The original XEX has a weakness. Ciphertext stealing provides support for sectors with size not divisible by block size...
30 KB (3,757 words) - 06:33, 9 September 2024
Block cipher mode of operation (redirect from Ciphertext feedback mode)
exist which have not been approved by NIST. For example, CTS is ciphertext stealing mode and available in many popular cryptographic libraries. The block...
52 KB (5,878 words) - 16:10, 12 September 2024
mode of operation of a block cipher. In tweaked-codebook mode with ciphertext stealing (XTS mode), it is one of the more popular modes of operation for...
4 KB (454 words) - 10:59, 19 June 2024
(CBC) or "xor–encrypt–xor (XEX)-based Tweaked codebook mode with ciphertext Stealing" (XTS) mode with a 128-bit or 256-bit key. CBC is not used over the...
36 KB (3,452 words) - 03:10, 17 August 2024
require padding. More intricate ways of ending a message such as ciphertext stealing or residual block termination avoid the need for padding. A disadvantage...
23 KB (3,307 words) - 18:11, 14 February 2024
Encryption (redirect from Ciphertexts)
the information, known as plaintext, into an alternative form known as ciphertext. Despite its goal, encryption does not itself prevent interference but...
34 KB (3,640 words) - 03:31, 10 September 2024
with the corresponding digit of the keystream, to give a digit of the ciphertext stream. Since encryption of each digit is dependent on the current state...
23 KB (2,213 words) - 15:26, 19 August 2024
abbreviation which may refer to: XEX-based tweaked-codebook mode with ciphertext stealing (XTS), a block cipher mode of operation used for full disk encryption...
466 bytes (99 words) - 18:29, 23 May 2023
City, Philippines The Calcutta Technical School, West Bengal, India Ciphertext stealing in cryptography Clear to send (disambiguation) control signal Common...
4 KB (479 words) - 01:16, 11 November 2023
cipher. Joan Daemen's 3-Way and BaseKing have unusual block sizes of 96 and 192 bits, respectively. Ciphertext stealing Format-preserving encryption...
3 KB (369 words) - 17:56, 21 May 2024
CipherSaber • Ciphertext expansion • Ciphertext indistinguishability • Ciphertext-only attack • Ciphertext stealing • CIPHERUNICORN-A • CIPHERUNICORN-E...
67 KB (2,933 words) - 23:58, 6 June 2024
Encryption Standard (XEX-based Tweaked CodeBook mode (TCB) with ciphertext stealing (CTS); the proper name should be XTC (XEX TCB CTS), but that acronym...
8 KB (852 words) - 02:14, 29 August 2024
Recommendation for Block Cipher Modes of Operation: Three Variants of Ciphertext Stealing for CBC Mode NIST Special Publication 800-38C, Recommendation for...
11 KB (1,424 words) - 14:36, 26 January 2024
converting readable information (plaintext) to unintelligible nonsense text (ciphertext), which can only be read by reversing the process (decryption). The sender...
98 KB (10,713 words) - 06:06, 10 September 2024
(TCB) with CipherText Stealing (CTS), the SISWG (IEEE P1619) standard for disk encryption. Authenticated encryption: Protection against ciphertext modification...
70 KB (2,826 words) - 01:56, 26 August 2024
trojan author and covertly broadcasts the resulting ciphertext. They mentioned that the ciphertext can be steganographically encoded and posted to a public...
45 KB (5,266 words) - 16:10, 5 July 2024
of random data (an unbreakable cipher like the one-time pad generates ciphertexts that look perfectly random without the private key). Examples of this...
50 KB (5,807 words) - 11:04, 17 August 2024
attacker encrypts the malicious code into a ciphertext, then includes the decryption method after the ciphertext. Detection of drive-by download attacks is...
8 KB (1,068 words) - 12:07, 11 August 2024
Digital rights management (redirect from Stealing ebooks)
systems share a common vulnerability: they provide their attackers with ciphertext, the cipher and the key. At this point, the secret isn't a secret anymore...
115 KB (11,200 words) - 03:55, 3 September 2024
"backwards", thus reversing all the substitutions. They then typed in the ciphertext and out came the plaintext. Better yet, several rotors can be placed such...
8 KB (1,099 words) - 22:20, 9 January 2024
authenticity of the data is ensured using a HMAC-SHA-256 hash of the ciphertext (Encrypt-then-MAC construction). KeePassX, a multi-platform open source...
17 KB (1,634 words) - 09:02, 28 August 2024
hybrid encryption and it results in a small asymmetric ciphertext as well as the symmetric ciphertext of the victim's data. It zeroizes the symmetric key...
105 KB (10,779 words) - 08:52, 7 September 2024
encryption (FPE), refers to encrypting in such a way that the output (the ciphertext) is in the same format as the input (the plaintext) Blinding is a cryptography...
27 KB (3,181 words) - 10:18, 8 August 2024
at rest, which leaves data vulnerable to attacks including stealing of ciphertext, cryptographic attack, attacks on encryption keys, destruction of encrypted...
6 KB (616 words) - 21:03, 6 March 2024
rotor machines which alter each character in the plaintext to produce the ciphertext, by means of a scrambler comprising a set of rotors that alter the electrical...
138 KB (17,741 words) - 21:17, 15 August 2024
large number of equivalents. However, this is at the cost of a very large ciphertext expansion.[original research?] A famous use of a book cipher is in the...
14 KB (1,985 words) - 02:05, 10 September 2024
operates by stealing bursts from its associated traffic channel. Bursts that carry FACCH data are distinguished from traffic bursts by stealing bits at each...
32 KB (5,116 words) - 01:42, 26 April 2024
of the Counter Barkan, Elad; Eli Biham; Nathan Keller (2003). "Instant Ciphertext-Only Cryptanalysis of GSM Encrypted Communication": 600–16. Archived from...
26 KB (3,542 words) - 14:58, 14 September 2024
at either end of the rotor series. In this case, by collecting enough ciphertext and applying a standard statistical method known as the kappa test, he...
26 KB (2,837 words) - 23:32, 1 September 2024