RSA (Rivest–Shamir–Adleman) is a public-key cryptosystem, one of the oldest widely used for secure data transmission. The initialism "RSA" comes from...
60 KB (7,790 words) - 07:32, 21 November 2024
Staphylococcus aureus RSA (cryptosystem) (Rivest–Shamir–Adleman), for public-key encryption RSA Conference, annual gathering RSA Factoring Challenge, for...
3 KB (417 words) - 11:24, 19 August 2024
public-key type of cryptosystem. A classical example of a cryptosystem is the Caesar cipher. A more contemporary example is the RSA cryptosystem. Another example...
4 KB (500 words) - 21:58, 21 October 2024
patent on the RSA cryptosystem technology granted in 1983. In 1994, RSA was against the Clipper chip during the Crypto War. In 1995, RSA sent a handful...
36 KB (3,678 words) - 11:01, 24 September 2024
eventual security of RSA-based cryptosystems—both for public-key encryption and digital signatures. More specifically, the RSA problem is to efficiently...
5 KB (681 words) - 04:22, 5 July 2023
security, compared to cryptosystems based on modular exponentiation in Galois fields, such as the RSA cryptosystem and ElGamal cryptosystem. Elliptic curves...
39 KB (4,674 words) - 12:50, 11 November 2024
libgcrypt LibreSSL mbed TLS Microsoft CryptoAPI OpenSSL wolfCrypt EdDSA RSA (cryptosystem) Johnson, Don; Menezes, Alfred (1999). "The Elliptic Curve Digital...
19 KB (2,833 words) - 03:20, 18 September 2024
invested effort in developing digital signature software based on the RSA cryptosystem.: 484 Nevertheless, NIST adopted DSA as a Federal standard (FIPS 186)...
16 KB (2,176 words) - 18:12, 30 July 2024
The Rabin cryptosystem is a family of public-key encryption schemes based on a trapdoor function whose security, like that of RSA, is related to the difficulty...
15 KB (2,399 words) - 19:36, 6 November 2023
included the following schemes: RSA cryptosystem (unbounded number of modular multiplications) ElGamal cryptosystem (unbounded number of modular multiplications)...
40 KB (4,409 words) - 00:38, 14 November 2024
Euler's theorem underlies the RSA cryptosystem, which is widely used in Internet communications. In this cryptosystem, Euler's theorem is used with n...
9 KB (1,149 words) - 18:09, 9 June 2024
ElGamal encryption (redirect from Elgamal discrete logarithm cryptosystem)
ElGamal cryptosystem is usually used as part of a hybrid cryptosystem, where the message itself is encrypted using a symmetric cryptosystem, and ElGamal...
10 KB (1,476 words) - 20:38, 7 September 2024
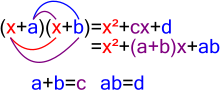
Euler's totient function (section The RSA cryptosystem)
is the order of the multiplicative group of integers modulo n. The RSA cryptosystem is based on this theorem: it implies that the inverse of the function...
44 KB (6,473 words) - 13:18, 17 October 2024
Public-key cryptography (redirect from Public-key cryptosystem)
provide both (e.g., RSA). Compared to symmetric encryption, asymmetric encryption can be too slow for many purposes. Today's cryptosystems (such as TLS, Secure...
36 KB (4,180 words) - 22:35, 12 October 2024
{\displaystyle E(m)\oplus t=m\oplus t\oplus S(k)=E(m\oplus t)} . In the RSA cryptosystem, a plaintext m {\displaystyle m} is encrypted as E ( m ) = m e mod...
6 KB (983 words) - 01:57, 16 January 2024
Coppersmith's attack (category Attacks on public-key cryptosystems)
the public-key cryptosystem RSA based on the Coppersmith method. Particular applications of the Coppersmith method for attacking RSA include cases when...
8 KB (1,466 words) - 05:54, 20 November 2024
received the message. Rabin's oblivious transfer scheme is based on the RSA cryptosystem. A more useful form of oblivious transfer called 1–2 oblivious transfer...
15 KB (2,019 words) - 04:07, 30 June 2024
Key encapsulation mechanism (section RSA)
cryptography, a key encapsulation mechanism, or KEM, is a public-key cryptosystem that allows a sender to generate a short secret key and transmit it to...
25 KB (3,047 words) - 06:13, 21 September 2024
Public-key cryptosystems use a public key for encryption and a private key for decryption. Diffie–Hellman key exchange RSA encryption Rabin cryptosystem Schnorr...
2 KB (120 words) - 03:36, 11 April 2022
the problem of factoring large integers, which is the basis of the RSA cryptosystem, widely used to secure internet communications. It follows that, presently...
15 KB (1,826 words) - 23:40, 18 November 2024
The Paillier cryptosystem, invented by and named after Pascal Paillier in 1999, is a probabilistic asymmetric algorithm for public key cryptography. The...
13 KB (1,929 words) - 21:01, 7 December 2023
Several specific public-key cryptosystems were then proposed by other researchers over the next few years, such as RSA in 1977 and Merkle-Hellman in...
10 KB (1,852 words) - 14:42, 11 November 2024
Wiener's attack (category Attacks on public-key cryptosystems)
modulus of N. In the RSA cryptosystem, Bob might tend to use a small value of d, rather than a large random number to improve the RSA decryption performance...
12 KB (1,759 words) - 16:06, 11 November 2024
Euclid in 300 BC, had no practical application before its use in the RSA cryptosystem, now widely used for the security of computer networks. In the 19th...
159 KB (15,698 words) - 18:01, 18 November 2024
much more difficult algorithmically, a fact which is exploited in the RSA cryptosystem to implement public-key cryptography. Polynomial factorization has...
41 KB (7,739 words) - 19:17, 12 November 2024
calculation is an important part of the application of semiprimes in the RSA cryptosystem. For a square semiprime n = p 2 {\displaystyle n=p^{2}} , the formula...
6 KB (859 words) - 01:51, 3 November 2024
hybrid cryptosystem to improve efficiency on long messages. Daniel Bleichenbacher. Chosen ciphertext attacks against protocols based on the RSA encryption...
7 KB (1,125 words) - 17:33, 23 July 2024
historical importance in showing the practical feasibility of the RSA cryptosystem. The Solovay–Strassen test is essentially an Euler–Jacobi probable...
10 KB (1,501 words) - 18:25, 18 November 2024
Cryptography (section Cryptosystems)
numbers, such as the RSA cryptosystem, require larger keys than elliptic curve techniques. For this reason, public-key cryptosystems based on elliptic curves...
99 KB (10,933 words) - 18:36, 19 November 2024
used in GM encryption is generated in the same manner as in the RSA cryptosystem. (See RSA, key generation for details.) Alice generates two distinct large...
7 KB (976 words) - 18:47, 24 August 2023