The GOST hash function, defined in the standards GOST R 34.11-94 and GOST 34.311-95 is a 256-bit cryptographic hash function. It was initially defined...
16 KB (2,206 words) - 02:44, 11 July 2024
revision of the standard, GOST R 34.12-2015 (RFC 7801, RFC 8891), specifies that it may be referred to as Magma. The GOST hash function is based on this cipher...
13 KB (1,339 words) - 18:53, 14 April 2024
Streebog (redirect from GOST R 34.11-2012)
hash function defined in the Russian national standard GOST R 34.11-2012 Information Technology – Cryptographic Information Security – Hash Function....
8 KB (854 words) - 06:39, 26 October 2024
Cryptanalysis of the GOST Hash Function. Crypto 2008. Xiaoyun Wang; Dengguo Feng; Xuejia Lai; Hongbo Yu (2004-08-17). "Collisions for Hash Functions MD4, MD5, HAVAL-128...
17 KB (1,055 words) - 12:18, 2 March 2023
Kupyna (category Cryptographic hash functions)
cryptographic hash function defined in the Ukrainian national standard DSTU 7564:2014. It was created to replace an obsolete GOST hash function defined in...
5 KB (540 words) - 11:14, 25 October 2024
The MD2 Message-Digest Algorithm is a cryptographic hash function developed by Ronald Rivest in 1989. The algorithm is optimized for 8-bit computers....
9 KB (1,053 words) - 18:49, 15 September 2024
BLAKE is a cryptographic hash function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants...
30 KB (2,848 words) - 05:59, 18 August 2024
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle...
48 KB (6,237 words) - 01:51, 13 November 2024
Fugue is a cryptographic hash function submitted by IBM to the NIST hash function competition. It was designed by Shai Halevi, William E. Hall, and Charanjit...
3 KB (654 words) - 03:06, 14 May 2024
HMAC (redirect from Keyed-Hashing Message Authentication)
type of message authentication code (MAC) involving a cryptographic hash function and a secret cryptographic key. As with any MAC, it may be used to simultaneously...
18 KB (2,327 words) - 04:57, 18 October 2024
Lane is a cryptographic hash function submitted to the NIST hash function competition; it was designed by Sebastiaan Indesteege with contributions by...
744 bytes (74 words) - 21:40, 5 February 2022
checksum. Hash function security summary Secure Hash Algorithms NIST hash function competition Key derivation functions (category) "Hash functions". www.azillionmonkeys...
10 KB (280 words) - 12:41, 17 October 2024
cryptographic hash function designed by Ross Anderson and Eli Biham in 1995 for efficiency on 64-bit platforms. The size of a Tiger hash value is 192 bits...
9 KB (910 words) - 14:47, 30 September 2023
The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S...
3 KB (464 words) - 07:05, 4 October 2024
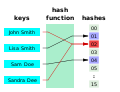
derived from a hash function which takes a data input and returns a fixed length of bits. Although hash algorithms, especially cryptographic hash algorithms...
9 KB (1,142 words) - 10:46, 9 November 2024
Skein is a cryptographic hash function and one of five finalists in the NIST hash function competition. Entered as a candidate to become the SHA-3 standard...
9 KB (836 words) - 02:45, 11 July 2024
cryptography, Whirlpool (sometimes styled WHIRLPOOL) is a cryptographic hash function. It was designed by Vincent Rijmen (co-creator of the Advanced Encryption...
11 KB (1,054 words) - 03:57, 19 March 2024
128-bit block cipher, defined in GOST R 34.12-2015 and RFC 7801. LION – block cypher built from stream cypher and hash function, by Ross Anderson LOKI89/91...
20 KB (1,899 words) - 15:57, 22 November 2024
SIMD is a cryptographic hash function based on the Merkle–Damgård construction submitted to the NIST hash function competition by Gaëtan Leurent. It is...
1 KB (127 words) - 13:39, 9 February 2023
ShangMi 3 (SM3) is a cryptographic hash function used in the Chinese National Standard. It was published by the National Cryptography Administration (Chinese:...
3 KB (287 words) - 17:06, 16 November 2023
hash function security/cryptanalysis can be found at hash function security summary. Basic general information about the cryptographic hash functions:...
16 KB (806 words) - 20:08, 6 August 2024
In cryptography, N-hash is a cryptographic hash function based on the FEAL round function, and is now considered insecure. It was proposed in 1990 in an...
2 KB (213 words) - 21:43, 31 December 2023
JH is a cryptographic hash function submitted to the NIST hash function competition by Hongjun Wu. Though chosen as one of the five finalists of the competition...
4 KB (399 words) - 18:44, 23 November 2024
Message authentication code (redirect from Keyed hash function)
different hashing primitive (SHA-1 and SHA-2) then XORed together to output the MAC. Universal hashing and in particular pairwise independent hash functions provide...
16 KB (1,914 words) - 13:54, 20 October 2024
The Password Hashing Competition was an open competition announced in 2013 to select one or more password hash functions that can be recognized as a recommended...
3 KB (254 words) - 01:08, 11 October 2023
multi-block-length hash function based on block ciphers" and typically achieves (asymptotic) rates between 1 and 2 independent of the hash size (only with...
24 KB (3,977 words) - 03:22, 7 June 2024
Yescrypt (category Cryptographic hash functions)
cryptographic key derivation function function used for password hashing on Fedora Linux, Debian, Ubuntu, and Arch Linux. The function is more resistant to offline...
2 KB (102 words) - 19:37, 17 November 2024
Merkle–Damgård construction (redirect from Merkle-Damgard hash function)
Merkle–Damgård hash function is a method of building collision-resistant cryptographic hash functions from collision-resistant one-way compression functions.: 145 ...
15 KB (1,904 words) - 18:20, 19 September 2024
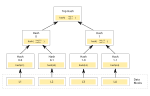
Merkle tree (redirect from Tiger-Tree Hash)
the above picture hash 0 is the result of hashing the concatenation of hash 0-0 and hash 0-1. That is, hash 0 = hash( hash 0-0 + hash 0-1 ) where "+" denotes...
15 KB (1,788 words) - 20:42, 10 September 2024