The Memory Machine is the debut studio album by Australian singer-songwriter Julia Stone. It was released in September 2010 in Australia and peaked at...
6 KB (358 words) - 14:02, 18 October 2022
In computing, memory ballooning is a technique that is used to eliminate the need to overcommit host memory used by virtual machines (VMs) by letting each...
2 KB (241 words) - 01:01, 9 May 2024
rules. Despite the model's simplicity, it is capable of implementing any computer algorithm. The machine operates on an infinite memory tape divided into...
74 KB (9,526 words) - 14:50, 20 August 2024
diffusion machine is a historical virtual shared memory architecture where data is free to migrate through the machine. Shared memory machines are convenient...
2 KB (209 words) - 20:36, 12 September 2015
machine they are hosted, or running on, actually has. This is possible because virtual machines (or processes) do not necessarily use as much memory at...
3 KB (261 words) - 14:18, 27 March 2023
processors access memory. Shared memory machines may be of the bus-based, extended, or hierarchical type. Distributed memory machines may have hypercube or mesh...
8 KB (968 words) - 16:27, 20 July 2024
distributed (shared) memory is that it is easier to design a machine that scales with the algorithm Distributed shared memory hides the mechanism of communication...
5 KB (582 words) - 16:38, 6 February 2024
data and machine code. A random-access memory device allows data items to be read or written in almost the same amount of time irrespective of the physical...
58 KB (5,942 words) - 19:18, 11 September 2024
Memories of Machines is a band formed by Tim Bowness (No-Man, Henry Fool) and Giancarlo Erra (Nosound) in April 2006. Memories of Machines emerged as a...
3 KB (282 words) - 15:13, 5 December 2022
and touring with the duo, Stone released her debut solo album, The Memory Machine, which charted on the ARIA Albums Chart into the top 100. It was well...
20 KB (1,644 words) - 23:30, 21 April 2024
Computer program (section Universal Turing machine)
each machine instruction. If the source code is requested for execution, then the operating system loads the corresponding interpreter into memory and...
127 KB (13,304 words) - 19:20, 12 September 2024
Instruction set architecture (redirect from Zero address machine)
Copy data from a memory location or a register to a memory location or a register (a machine instruction is often called move; however, the term is misleading)...
35 KB (4,286 words) - 10:10, 8 September 2024
data in the CPU's registers or memory. Early CPUs had specific machine code that might break backward compatibility with each new CPU released. The notion...
31 KB (3,477 words) - 14:35, 8 September 2024
Hotel Diablo (redirect from Burning Memories (Machine Gun Kelly song))
is the fourth studio album by American rapper Machine Gun Kelly. It was released on July 5, 2019, via Bad Boy Records and Interscope Records. The album...
27 KB (2,192 words) - 07:41, 12 August 2024
are actually available on a given machine" which "creates the illusion to users of a very large (main) memory". The computer's operating system, using...
38 KB (4,698 words) - 00:24, 17 January 2024
The Wayback Machine is a digital archive of the World Wide Web founded by the Internet Archive, an American nonprofit organization based in San Francisco...
76 KB (7,073 words) - 14:25, 10 September 2024
Computer memory stores information, such as data and programs, for immediate use in the computer. The term memory is often synonymous with the terms RAM...
29 KB (3,284 words) - 18:53, 5 September 2024
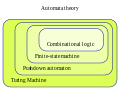
Turing completeness (category Turing machine)
be functionally analyzed like a single-tape Turing machine (which uses a "tape" for memory); thus the associated mathematics can apply by abstracting their...
29 KB (3,163 words) - 23:27, 21 May 2024
Eidetic memory (/aɪˈdɛtɪk/ eye-DET-ik), also known as photographic memory and total recall, is the ability to recall an image from memory with high precision—at...
22 KB (2,603 words) - 01:26, 12 August 2024
than the entire device. NOR flash memory allows a single machine word to be written – to an erased location – or read independently. A flash memory device...
186 KB (17,049 words) - 13:05, 13 September 2024
A memory leak may also happen when an object is stored in memory but cannot be accessed by the running code (i.e. unreachable memory). A memory leak...
19 KB (2,718 words) - 06:28, 1 June 2024
non-volatile random access memory (NVRAM) or even stored on CD-ROM or DVD, depending on the capabilities of the machine and the applicable regulations. Based...
78 KB (10,571 words) - 02:29, 8 August 2024
A machine is a physical system that uses power to apply forces and control movement to perform an action. The term is commonly applied to artificial devices...
57 KB (6,396 words) - 21:39, 22 August 2024
that mirror human thought processes. By the early 1960s an experimental "learning machine" with punched tape memory, called Cybertron, had been developed...
135 KB (14,773 words) - 10:00, 12 September 2024
Parallel RAM (redirect from Parallel random access machine)
parallel random-access machine (parallel RAM or PRAM) is a shared-memory abstract machine. As its name indicates, the PRAM is intended as the parallel-computing...
11 KB (1,275 words) - 08:57, 12 August 2024
Computer (redirect from Computing machine)
are stored in memory. Von Neumann acknowledged that the central concept of the modern computer was due to this paper. Turing machines are to this day...
135 KB (13,742 words) - 06:03, 5 September 2024
to the same memory address. Counter machines with three counters can compute any partial recursive function of a single variable. Counter machines with...
55 KB (4,697 words) - 05:11, 13 June 2024
can allot the host machine's registers for the top several operands of the stack instead of the host machine's memory In a stack machine, the operands...
48 KB (5,809 words) - 08:41, 15 May 2024
because an FSM's memory is limited by the number of states it has. A finite-state machine has the same computational power as a Turing machine that is restricted...
41 KB (4,540 words) - 20:01, 16 August 2024
Cold boot attack (redirect from Full memory encryption)
a computer performs a memory dump of a computer's random-access memory (RAM) by performing a hard reset of the target machine. Typically, cold boot attacks...
38 KB (4,246 words) - 03:19, 31 July 2024