output. The values returned by a hash function are called hash values, hash codes, (hash/message) digests, or simply hashes. The values are usually used to...
50 KB (7,467 words) - 11:20, 14 April 2025
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle...
49 KB (6,299 words) - 21:20, 2 April 2025
checksum. Hash function security summary Secure Hash Algorithms NIST hash function competition Key derivation functions (category) "Hash functions". www.azillionmonkeys...
10 KB (279 words) - 08:17, 17 April 2025
In computer science, a perfect hash function h for a set S is a hash function that maps distinct elements in S to a set of m integers, with no collisions...
23 KB (2,870 words) - 13:49, 29 March 2025
cryptography, Whirlpool (sometimes styled WHIRLPOOL) is a cryptographic hash function. It was designed by Vincent Rijmen (co-creator of the Advanced Encryption...
11 KB (1,054 words) - 03:57, 19 March 2024
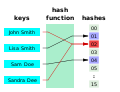
data type that maps keys to values. A hash table uses a hash function to compute an index, also called a hash code, into an array of buckets or slots...
53 KB (5,944 words) - 17:05, 28 March 2025
The Secure Hash Algorithms are a family of cryptographic hash functions published by the National Institute of Standards and Technology (NIST) as a U.S...
3 KB (464 words) - 07:05, 4 October 2024
BLAKE is a cryptographic hash function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants...
30 KB (2,855 words) - 02:58, 11 January 2025
password, or a passphrase using a pseudorandom function (which typically uses a cryptographic hash function or block cipher). KDFs can be used to stretch...
13 KB (1,640 words) - 13:55, 21 February 2025
hash >> 6; } hash += hash << 3; hash ^= hash >> 11; hash += hash << 15; return hash; } Sample hash values for one_at_a_time hash function. one_at_a_time("a"...
7 KB (852 words) - 21:39, 4 May 2024
The MD2 Message-Digest Algorithm is a cryptographic hash function developed by Ronald Rivest in 1989. The algorithm is optimized for 8-bit computers....
9 KB (1,053 words) - 04:19, 31 December 2024
hash function security/cryptanalysis can be found at hash function security summary. Basic general information about the cryptographic hash functions:...
16 KB (806 words) - 20:08, 6 August 2024
non-cryptographic hash functions (NCHFs) are hash functions intended for applications that do not need the rigorous security requirements of the cryptographic hash functions...
7 KB (796 words) - 11:21, 5 March 2025
is a non-cryptographic hash function created by Glenn Fowler, Landon Curt Noll, and Kiem-Phong Vo. The basis of the FNV hash algorithm was taken from...
15 KB (1,358 words) - 15:56, 7 April 2025
cryptographic hash function designed by Ross Anderson and Eli Biham in 1995 for efficiency on 64-bit platforms. The size of a Tiger hash value is 192 bits...
9 KB (910 words) - 14:47, 30 September 2023
HMAC (redirect from Keyed-Hashing Message Authentication)
type of message authentication code (MAC) involving a cryptographic hash function and a secret cryptographic key. As with any MAC, it may be used to simultaneously...
18 KB (2,314 words) - 18:51, 16 April 2025
universal hashing (in a randomized algorithm or data structure) refers to selecting a hash function at random from a family of hash functions with a certain...
29 KB (4,885 words) - 22:53, 23 December 2024
PJW hash function is a non-cryptographic hash function created by Peter J. Weinberger of AT&T Bell Labs. A variant of PJW hash had been used to create...
2 KB (263 words) - 12:47, 25 October 2024
cryptographic hash functions. Note that not all entries may be up to date. For a summary of other hash function parameters, see comparison of cryptographic hash functions...
17 KB (1,063 words) - 22:58, 15 March 2025
Preimage attack (redirect from Hash function preimage)
attack on cryptographic hash functions tries to find a message that has a specific hash value. A cryptographic hash function should resist attacks on...
7 KB (895 words) - 15:44, 13 April 2024
JH is a cryptographic hash function submitted to the NIST hash function competition by Hongjun Wu. Though chosen as one of the five finalists of the competition...
4 KB (399 words) - 17:35, 7 January 2025
Rainbow table (redirect from Reduction function)
cryptographic hash function, usually for cracking password hashes. Passwords are typically stored not in plain text form, but as hash values. If such...
24 KB (3,485 words) - 19:40, 2 April 2025
Message authentication code (redirect from Keyed hash function)
different hashing primitive (SHA-1 and SHA-2) then XORed together to output the MAC. Universal hashing and in particular pairwise independent hash functions provide...
16 KB (1,918 words) - 17:55, 22 January 2025
information, called the trapdoor, is known. A collision-free hash function f is a one-way function that is also collision-resistant; that is, no randomized...
14 KB (1,956 words) - 16:22, 30 March 2025
derived from a hash function which takes a data input and returns a fixed length of bits. Although hash algorithms, especially cryptographic hash algorithms...
9 KB (1,142 words) - 10:46, 9 November 2024
ShangMi 3 (SM3) is a cryptographic hash function, standardised for use in commercial cryptography in China. It was published by the National Cryptography...
4 KB (335 words) - 01:57, 15 December 2024
cryptography, cryptographic hash functions can be divided into two main categories. In the first category are those functions whose designs are based on...
14 KB (1,823 words) - 18:28, 7 January 2025
In computer science, locality-sensitive hashing (LSH) is a fuzzy hashing technique that hashes similar input items into the same "buckets" with high probability...
30 KB (4,024 words) - 17:28, 16 April 2025
Salt (cryptography) (redirect from Salted hash)
cryptography, a salt is random data fed as an additional input to a one-way function that hashes data, a password or passphrase. Salting helps defend against attacks...
13 KB (1,533 words) - 12:18, 19 January 2025
Merkle tree (redirect from Tiger-Tree Hash)
the above picture hash 0 is the result of hashing the concatenation of hash 0-0 and hash 0-1. That is, hash 0 = hash( hash 0-0 + hash 0-1 ) where "+" denotes...
15 KB (1,790 words) - 06:31, 3 March 2025