Cryptography, or cryptology (from Ancient Greek: κρυπτός, romanized: kryptós "hidden, secret"; and γράφειν graphein, "to write", or -λογία -logia, "study"...
99 KB (10,936 words) - 05:39, 24 November 2024
Public-key cryptography, or asymmetric cryptography, is the field of cryptographic systems that use pairs of related keys. Each key pair consists of a...
40 KB (4,507 words) - 23:07, 24 November 2024
Post-quantum cryptography (PQC), sometimes referred to as quantum-proof, quantum-safe, or quantum-resistant, is the development of cryptographic algorithms...
62 KB (6,467 words) - 07:58, 19 November 2024
A key in cryptography is a piece of information, usually a string of numbers or letters that are stored in a file, which, when processed through a cryptographic...
13 KB (1,506 words) - 20:06, 18 October 2024
In cryptography, a salt is random data fed as an additional input to a one-way function that hashes data, a password or passphrase. Salting helps defend...
13 KB (1,533 words) - 23:19, 23 October 2024
Elliptic-curve cryptography (ECC) is an approach to public-key cryptography based on the algebraic structure of elliptic curves over finite fields. ECC...
39 KB (4,670 words) - 04:30, 23 November 2024
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle...
48 KB (6,237 words) - 01:51, 13 November 2024
Encryption (redirect from Cryptographic algorithm)
In cryptography, encryption is the process of transforming (more specifically, encoding) information in a way that, ideally, only authorized parties can...
35 KB (3,687 words) - 11:44, 15 November 2024
Quantum cryptography is the science of exploiting quantum mechanical properties to perform cryptographic tasks. The best known example of quantum cryptography...
81 KB (9,042 words) - 15:37, 28 October 2024
Symmetric-key algorithm (redirect from Symmetric key cryptography)
Symmetric-key algorithms are algorithms for cryptography that use the same cryptographic keys for both the encryption of plaintext and the decryption of...
15 KB (1,544 words) - 20:48, 3 November 2024
and topical guide to cryptography: Cryptography (or cryptology) – practice and study of hiding information. Modern cryptography intersects the disciplines...
20 KB (1,899 words) - 15:57, 22 November 2024
Strong cryptography or cryptographically strong are general terms used to designate the cryptographic algorithms that, when used correctly, provide a very...
22 KB (2,846 words) - 07:57, 27 March 2024
Cryptography, the use of codes and ciphers to protect secrets, began thousands of years ago. Until recent decades, it has been the story of what might...
51 KB (6,711 words) - 13:01, 11 November 2024
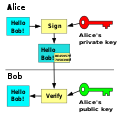
Alice and Bob (redirect from Characters in cryptography)
fictional characters commonly used as placeholders in discussions about cryptographic systems and protocols, and in other science and engineering literature...
24 KB (2,023 words) - 15:16, 20 November 2024
The export of cryptography is the transfer from one country to another of devices and technology related to cryptography. In the early days of the Cold...
2 KB (190 words) - 23:55, 8 June 2024
Cryptanalysis (redirect from Cryptographic attack)
is used to breach cryptographic security systems and gain access to the contents of encrypted messages, even if the cryptographic key is unknown. In...
44 KB (5,215 words) - 23:19, 22 November 2024
A cryptographic protocol is an abstract or concrete protocol that performs a security-related function and applies cryptographic methods, often as sequences...
9 KB (1,009 words) - 10:38, 7 October 2024
Visual cryptography is a cryptographic technique which allows visual information (pictures, text, etc.) to be encrypted in such a way that the decrypted...
11 KB (1,412 words) - 17:32, 20 November 2024
RSA (cryptosystem) (redirect from RSA public key cryptography)
"Introduction to Cryptography with Open-Source Software". p. 12. Surender R. Chiluka. "Public key Cryptography". Neal Koblitz. "Cryptography As a Teaching...
60 KB (7,790 words) - 07:32, 21 November 2024
PKCS (redirect from Public-Key Cryptography Standards)
In cryptography, PKCS (Public Key Cryptography Standards) are a group of public-key cryptography standards devised and published by RSA Security LLC,...
10 KB (289 words) - 10:46, 24 June 2024
Diffie–Hellman key exchange (redirect from New Directions in Cryptography)
exchange is a mathematical method of securely generating a symmetric cryptographic key over a public channel and was one of the first public-key protocols...
48 KB (5,262 words) - 08:24, 14 November 2024
Elliptic Curve Digital Signature Algorithm (category Public-key cryptography)
In cryptography, the Elliptic Curve Digital Signature Algorithm (ECDSA) offers a variant of the Digital Signature Algorithm (DSA) which uses elliptic-curve...
19 KB (2,833 words) - 03:20, 18 September 2024
Digital signature (redirect from Cryptographic signature)
to the recipient. Digital signatures are a standard element of most cryptographic protocol suites, and are commonly used for software distribution, financial...
45 KB (5,315 words) - 14:52, 6 November 2024
Classical cipher (redirect from Classical cryptography)
In cryptography, a classical cipher is a type of cipher that was used historically but for the most part, has fallen into disuse. In contrast to modern...
15 KB (2,528 words) - 02:24, 15 June 2024
Key size (redirect from Cryptography/key length)
In cryptography, key size or key length refers to the number of bits in a key used by a cryptographic algorithm (such as a cipher). Key length defines...
29 KB (3,213 words) - 18:15, 18 September 2024
discussions about cryptography and related issues. sci.crypt — an unmoderated forum for discussions on technical aspects of cryptography. sci.crypt.research...
2 KB (214 words) - 18:22, 29 April 2024
(India), SCU13 and SCU14. The cryptographic element of each SLU was supplied by the RAF and was based on the TYPEX cryptographic machine and one-time pad systems...
78 KB (10,348 words) - 09:16, 15 November 2024
BLS digital signature (redirect from BLS (Cryptography))
BLS digital signature, also known as Boneh–Lynn–Shacham (BLS), is a cryptographic signature scheme which allows a user to verify that a signer is authentic...
8 KB (950 words) - 05:35, 23 November 2024
In cryptography, snake oil is any cryptographic method or product considered to be bogus or fraudulent. The name derives from snake oil, one type of patent...
5 KB (545 words) - 17:56, 14 November 2024
In cryptography, padding is any of a number of distinct practices which all include adding data to the beginning, middle, or end of a message prior to...
23 KB (3,307 words) - 18:11, 14 February 2024