Network Computer Reference Profile (NC reference profile, NCRP) was a specification for a network computer put forward by Oracle Corporation, endorsed...
4 KB (377 words) - 20:02, 27 March 2023
based on the Network Computer Reference Profile. The brand was also employed as a marketing term to try to popularize this design of computer within enterprise...
13 KB (1,375 words) - 01:04, 26 April 2024
implementation of the Network Computer Reference Profile that Oracle Corporation commissioned Acorn to specify for network computers (for more detail on...
12 KB (998 words) - 20:06, 18 August 2023
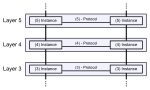
OSI model (redirect from Open Systems Interconnection--Reference Model)
the OSI reference model, the communications between systems are split into seven different abstraction layers: Physical, Data Link, Network, Transport...
55 KB (5,647 words) - 06:22, 30 August 2024
Apple Pippin (section Network Computer Platform)
build computers that are designed around the Network Computer platform. The idea was to design technology based on a Network Computer Reference Profile including...
60 KB (5,234 words) - 21:58, 9 June 2024
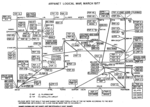
ARPANET (redirect from Advanced Research Projects Agency Network)
Projects Agency Network (ARPANET) was the first wide-area packet-switched network with distributed control and one of the first computer networks to implement...
91 KB (9,994 words) - 03:05, 9 August 2024
Mac NC (category Network computer (brand))
intent to build computers that are designed around the "network computer platform". Products based on the Network Computer Reference Profile include diskless...
4 KB (438 words) - 03:32, 26 May 2023
the entire color range to allow for different gamuts. The reference illuminant of the Profile connection space (PCS) is a 16-bit fractional approximation...
9 KB (1,139 words) - 15:01, 15 April 2024
National Council on Radiation Protection and Measurements, USA Network Computer Reference Profile National Committee for Responsive Philanthropy This disambiguation...
225 bytes (56 words) - 08:39, 1 May 2020
defined loss function. This method allows the network to generalize to unseen data. Historically, digital computers evolved from the von Neumann model, and...
153 KB (16,008 words) - 01:30, 23 August 2024
continue beyond in-person interactions. These computer mediated interactions link members of various networks and may help to create, sustain and develop...
123 KB (13,497 words) - 07:16, 28 August 2024
roaming user profile is a file synchronization concept in the Windows NT family of operating systems that allows users with a computer joined to a Windows...
31 KB (4,176 words) - 04:46, 29 May 2024
Packet switching (redirect from Packet-switched computer network)
Packet switching is the primary basis for data communications in computer networks worldwide. During the early 1960s, American engineer Paul Baran developed...
158 KB (16,975 words) - 17:49, 29 August 2024
the reference transaction is a computer-mediated communication. It is the remote, computer-mediated delivery of reference information provided by library...
23 KB (2,958 words) - 22:55, 12 December 2023
Internet (redirect from Global computer network)
interconnected computer networks that uses the Internet protocol suite (TCP/IP) to communicate between networks and devices. It is a network of networks that consists...
155 KB (16,435 words) - 22:23, 27 August 2024
An analog computer or analogue computer is a type of computation machine (computer) that uses the continuous variation aspect of physical phenomena such...
56 KB (6,932 words) - 06:49, 26 August 2024
user population is profiled for each tool, ability for users to edit their own profile data and type of networking. Active networking means that the user...
70 KB (1,636 words) - 21:10, 3 August 2024
field is significant due to the expanded reliance on computer systems, the Internet, and wireless network standards. It is also significant due to the growth...
219 KB (22,183 words) - 17:09, 27 August 2024
Precision Time Protocol (category Network time-related software)
is a protocol used to synchronize clocks throughout a computer network. On a local area network, it achieves clock accuracy in the sub-microsecond range...
27 KB (3,357 words) - 20:22, 27 August 2024
In computer networking, a network service is an application running at the network application layer and above, that provides data storage, manipulation...
4 KB (496 words) - 14:10, 13 May 2024
Network access control (NAC) is an approach to computer security that attempts to unify endpoint security technology (such as antivirus, host intrusion...
11 KB (1,420 words) - 23:20, 27 April 2024
ISCSI (redirect from Internet Small Computer Systems Interface)
Internet Small Computer Systems Interface or iSCSI (/aɪˈskʌzi/ eye-SKUZ-ee) is an Internet Protocol-based storage networking standard for linking data...
26 KB (3,244 words) - 16:17, 8 August 2024
Security hacker (redirect from Computer hackers)
methods for breaching defenses and exploiting weaknesses in a computer system or network. Hackers may be motivated by a multitude of reasons, such as profit...
55 KB (5,981 words) - 21:25, 14 August 2024
program, but is no longer referenced; such memory is called garbage. Garbage collection was invented by American computer scientist John McCarthy around...
39 KB (4,028 words) - 04:48, 28 June 2024
Java Platform, Micro Edition (redirect from Foundation Profile)
version 47.0). Oracle provides a reference implementation of the specification, and some configurations and profiles for MIDP and CDC. Starting with the...
19 KB (1,436 words) - 07:59, 30 August 2024
Library (redirect from Reference library)
network) to thwart mass surveillance. Libraries can have several different spaces for different functions such as: Auditorium / Lecture hall Computer...
71 KB (7,578 words) - 14:08, 12 August 2024
NCOS (redirect from Network Computer Operating System)
RISC OS-NC and RO-STB. NCOS was designed in accord with the Network Computer Reference Profile and thus supports internet standards of the time.[citation...
9 KB (713 words) - 11:20, 5 October 2023
Intrusion detection system (redirect from Network intrusion detection system)
IDS types range in scope from single computers to large networks. The most common classifications are network intrusion detection systems (NIDS) and...
46 KB (5,573 words) - 22:27, 1 August 2024
Authentication, authorization, and accounting (redirect from AAA (Computer security))
accounting (AAA) is a framework used to control and track access within a computer network. Authentication is concerned with proving identity, authorization with...
5 KB (558 words) - 19:36, 5 August 2024
Ubiquitous computing (redirect from Ubiquitous computer)
mobile codes, sensors, microprocessors, new I/Os and user interfaces, computer networks, mobile protocols, global navigational systems, and new materials...
20 KB (1,966 words) - 22:58, 14 August 2024