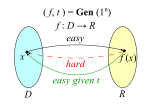
In theoretical computer science and cryptography, a trapdoor function is a function that is easy to compute in one direction, yet difficult to compute...
9 KB (1,316 words) - 00:34, 25 June 2024
mills, however, its list of uses has grown over time. The trapdoor has played a pivotal function in the operation of the gallows, cargo ships, trains, booby...
6 KB (590 words) - 13:38, 8 August 2024
existence of one-way functions. A trapdoor one-way function or trapdoor permutation is a special kind of one-way function. Such a function is hard to invert...
14 KB (1,947 words) - 21:40, 27 September 2024
based on a trapdoor function whose security, like that of RSA, is related to the difficulty of integer factorization. The Rabin trapdoor function has the...
15 KB (2,399 words) - 19:36, 6 November 2023
A cryptographic hash function (CHF) is a hash algorithm (a map of an arbitrary binary string to a binary string with a fixed size of n {\displaystyle n}...
48 KB (6,237 words) - 06:56, 21 October 2024
variant of the learning with errors lattice problem as its basic trapdoor function. It won the NIST competition for the first post-quantum cryptography...
14 KB (1,416 words) - 19:09, 20 October 2024
In cryptography, a pseudorandom function family, abbreviated PRF, is a collection of efficiently-computable functions which emulate a random oracle in...
8 KB (1,023 words) - 14:10, 31 January 2024
one-way trapdoor function and a random function (hash function); EPOC-2 uses a one-way trapdoor function, two random functions (hash functions) and a symmetric-key...
3 KB (323 words) - 22:25, 27 February 2024
In cryptography, a key derivation function (KDF) is a cryptographic algorithm that derives one or more secret keys from a secret value such as a master...
13 KB (1,635 words) - 18:38, 20 October 2024
Key management Key size Public-key cryptography Rabin cryptosystem Trapdoor function Namely, the values of m which are equal to −1, 0, or 1 modulo p while...
60 KB (7,774 words) - 17:45, 21 October 2024
Rainbow table (redirect from Reduction function)
is a precomputed table for caching the outputs of a cryptographic hash function, usually for cracking password hashes. Passwords are typically stored not...
24 KB (3,485 words) - 04:38, 19 October 2024
Perhaps the first system with complete threshold properties for a trapdoor function (such as RSA) and a proof of security was published in 1994 by Alfredo...
8 KB (868 words) - 22:39, 15 March 2024
Feistel cipher (redirect from F-function)
similar operations, and both consist of iteratively running a function called a "round function" a fixed number of times. Many modern symmetric block ciphers...
10 KB (1,316 words) - 23:55, 19 August 2024
Typically a Schnorr group is used. All users agree on a cryptographic hash function H : { 0 , 1 } ∗ → Z / q Z {\displaystyle H:\{0,1\}^{*}\rightarrow \mathbb...
8 KB (1,204 words) - 18:16, 2 October 2024
schemes. The first such scheme which is not built on trapdoor functions but rather on a family of function with a much weaker required property of one-way...
45 KB (5,292 words) - 15:11, 30 September 2024
key from x k {\displaystyle x_{k}} using some hash-based key derivation function. The shared secret calculated by both parties is equal, because d A ⋅ Q...
13 KB (2,065 words) - 19:12, 14 October 2024
secret Trapdoor function Trusted timestamping Key-based routing Onion routing Garlic routing Kademlia Mix network Mathematics Cryptographic hash function Block...
4 KB (443 words) - 12:38, 16 June 2024
Yescrypt (category Cryptographic hash functions)
cryptographic key derivation function function used for password hashing on Fedora Linux, Debian, Ubuntu, and Arch Linux. The function is more resistant to offline...
2 KB (102 words) - 08:19, 12 July 2024
"disguised" version of W {\displaystyle W} . The private key also contains some "trapdoor" information that can be used to transform a hard knapsack problem using...
10 KB (1,838 words) - 00:16, 24 August 2024
secret Trapdoor function Trusted timestamping Key-based routing Onion routing Garlic routing Kademlia Mix network Mathematics Cryptographic hash function Block...
4 KB (321 words) - 08:54, 15 September 2024
Preimage attack (redirect from Hash function preimage)
attack on cryptographic hash functions tries to find a message that has a specific hash value. A cryptographic hash function should resist attacks on its...
7 KB (895 words) - 15:44, 13 April 2024
plaintext prior to asymmetric encryption. When combined with any secure trapdoor one-way permutation f {\displaystyle f} , this processing is proved in...
9 KB (1,460 words) - 17:38, 1 June 2024
secret Trapdoor function Trusted timestamping Key-based routing Onion routing Garlic routing Kademlia Mix network Mathematics Cryptographic hash function Block...
10 KB (1,198 words) - 06:02, 16 September 2024
cryptography, Whirlpool (sometimes styled WHIRLPOOL) is a cryptographic hash function. It was designed by Vincent Rijmen (co-creator of the Advanced Encryption...
11 KB (1,054 words) - 03:57, 19 March 2024
BLAKE is a cryptographic hash function based on Daniel J. Bernstein's ChaCha stream cipher, but a permuted copy of the input block, XORed with round constants...
30 KB (2,848 words) - 05:59, 18 August 2024
collision resistant" hash functions; it was employed to construct general digital signature schemes without trapdoor functions, and also within chosen-ciphertext...
2 KB (324 words) - 14:32, 6 February 2024
public key. Fingerprints are created by applying a cryptographic hash function to a public key. Since fingerprints are shorter than the keys they refer...
9 KB (1,286 words) - 15:11, 13 August 2023
Security level (redirect from Broken hash function)
the strength that a cryptographic primitive — such as a cipher or hash function — achieves. Security level is usually expressed as a number of "bits of...
13 KB (1,360 words) - 04:38, 10 May 2024
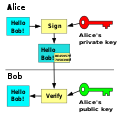
problem in a gap Diffie–Hellman group. A signature scheme consists of three functions: generate, sign, and verify. Key generation The key generation algorithm...
8 KB (823 words) - 20:29, 3 October 2024
Argon2 (category Key derivation functions)
Argon2 is a key derivation function that was selected as the winner of the 2015 Password Hashing Competition. It was designed by Alex Biryukov, Daniel...
14 KB (1,491 words) - 06:28, 21 August 2024