In cryptography, CIPHERUNICORN-E is a block cipher created by NEC in 1998. It was among the cryptographic techniques recommended for Japanese government...
3 KB (285 words) - 07:18, 27 April 2022
Symmetric key ciphers 64-bit block ciphers CIPHERUNICORN-E Hierocrypt-L1 MISTY1 128-bit block ciphers CIPHERUNICORN-A CLEFIA Hierocrypt-3 Stream ciphers Enocoro-128v2...
8 KB (974 words) - 00:22, 19 August 2023
In cryptography, CIPHERUNICORN-A is a block cipher created by NEC in 2000. It was among the cryptographic techniques recommended for Japanese government...
3 KB (307 words) - 22:02, 25 March 2022
is a derangement), i.e., S ( a i , j ) ≠ a i , j {\displaystyle S(a_{i,j})\neq a_{i,j}} , and also any opposite fixed points, i.e., S ( a i , j ) ⊕ a i...
49 KB (5,595 words) - 00:02, 27 August 2024
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
12 KB (1,524 words) - 16:41, 5 September 2024
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
10 KB (1,316 words) - 23:55, 19 August 2024
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
10 KB (1,040 words) - 02:50, 11 January 2024
receiver. Message authentication codes can be constructed from an AEAD cipher (e.g. AES-GCM). However, symmetric ciphers cannot be used for non-repudiation...
15 KB (1,544 words) - 02:53, 7 June 2024
combined with an initialization vector (IV) and encrypted with a block cipher E, usually AES. The result of this encryption is then XORed with the plaintext...
23 KB (2,996 words) - 08:23, 11 September 2024
for the sender, "Bob" (or "B") for the intended recipient, and "Eve" (or "E") for the eavesdropping adversary. Since the development of rotor cipher machines...
98 KB (10,713 words) - 06:06, 10 September 2024
misconception is to use inverse order of encryption as decryption algorithm (i.e. first XORing P17 and P18 to the ciphertext block, then using the P-entries...
17 KB (1,895 words) - 03:39, 19 August 2024
doi:10.1007/s00145-021-09398-9. eISSN 1432-1378. hdl:2066/235128. ISSN 0933-2790. S2CID 253633576. TU Graz. "Ascon: Publications". tugraz.at. v t e...
8 KB (848 words) - 03:29, 28 April 2024
regulations historically restricted key lengths to 56-bit symmetric keys (e.g. Data Encryption Standard), these restrictions are no longer in place, so...
21 KB (2,250 words) - 15:26, 19 July 2024
a message to obscure the fact that many messages end in predictable ways, e.g. sincerely yours. Official messages often start and end in predictable ways:...
23 KB (3,307 words) - 18:11, 14 February 2024
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
8 KB (924 words) - 10:55, 17 July 2024
is commonly called a nonce (a number used only once), and the primitives (e.g. CBC) are considered stateful rather than randomized. This is because an...
14 KB (1,797 words) - 08:53, 7 September 2024
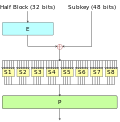
function of encryption, i.e., D = E−1. More formally, a block cipher is specified by an encryption function E K ( P ) := E ( K , P ) : { 0 , 1 } k × {...
50 KB (6,475 words) - 03:59, 22 August 2024
{\displaystyle K_{2}} : E K 1 ( E K 2 ( P ) ) = P {\displaystyle E_{K_{1}}(E_{K_{2}}(P))=P} or equivalently, E K 2 = D K 1 . {\displaystyle E_{K_{2}}=D_{K_{1}}...
59 KB (6,541 words) - 09:32, 30 July 2024
K2)} instead of one, and encrypt each block twice: E K 2 ( E K 1 ( plaintext ) ) {\displaystyle E_{K2}(E_{K1}({\textrm {plaintext}}))} . If the original...
23 KB (2,946 words) - 08:25, 17 May 2024
such as using a sequential counter over the block prior to encryption (i.e., CTR mode) and removing it after decryption avoids this problem. Another...
12 KB (1,295 words) - 08:30, 9 August 2024
and a candidate for the AES competition CIPHERUNICORN-A – 128-bit block; CRYPTREC recommendation CIPHERUNICORN-E – 64-bit block; CRYPTREC recommendation...
20 KB (1,890 words) - 03:11, 18 August 2024
Index of cryptography articles (section E)
indistinguishability • Ciphertext-only attack • Ciphertext stealing • CIPHERUNICORN-A • CIPHERUNICORN-E • Classical cipher • Claude Shannon • Claw-free permutation...
67 KB (2,933 words) - 23:58, 6 June 2024
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
3 KB (218 words) - 20:16, 20 April 2023
slightly (for example, flipping a single bit), the output changes significantly (e.g., half the output bits flip). In the case of high-quality block ciphers...
5 KB (568 words) - 17:23, 14 December 2023
This compression function is easily invertible if the data block is known, i.e. given the data block on which it acted and the output of the compression...
9 KB (903 words) - 07:08, 27 April 2022
standards, raised considerable speculation about whether NSA had found weaknesses e.g. in elliptic-curve algorithms or others, or was trying to distance itself...
9 KB (635 words) - 23:58, 26 August 2024
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
10 KB (1,031 words) - 05:27, 28 February 2023
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
3 KB (402 words) - 17:31, 15 March 2023
a constant difference. Difference can be defined in several ways, but the eXclusive OR (XOR) operation is usual. The attacker then computes the differences...
13 KB (1,688 words) - 16:36, 5 September 2024
BaseKing BassOmatic BATON BEAR and LION CAST-256 Chiasmus CIKS-1 CIPHERUNICORN-A CIPHERUNICORN-E CLEFIA CMEA Cobra COCONUT98 Crab Cryptomeria/C2 CRYPTON CS-Cipher...
5 KB (688 words) - 07:27, 20 November 2023